Jun 09, 2018 Most Linux and Unix distribution create ssh keys for you during the installation of the OpenSSH server package. But it may be useful to be able re-generate new server keys from time to time. For example, when you duplicate VM (KVM or container) which contains an installed ssh package and you need to use different keys from cloned KVM VM guest. Ubuntu Main amd64 Official openssh-server7.6p1-4amd64.deb: secure shell (SSH) server, for secure access from remote machines: Ubuntu Main arm64 Official openssh-server7.6p1-4arm64.deb.
Most authentication in Windows environments is done with a username-password pair.This works well for systems that share a common domain.When working across domains, such as between on-premise and cloud-hosted systems, it becomes vulnerable to brute force intrusions.
By comparison, Linux environments commonly use public-key/private-key pairs to drive authentication which doesn't require the use of guessable passwords.OpenSSH includes tools to help support this, specifically:
- ssh-keygen for generating secure keys
- ssh-agent and ssh-add for securely storing private keys
- scp and sftp to securely copy public key files during initial use of a server
This document provides an overview of how to use these tools on Windows to begin using key authentication with SSH.If you are unfamiliar with SSH key management, we strongly recommend you review NIST document IR 7966 titled 'Security of Interactive and Automated Access Management Using Secure Shell (SSH).'
Openssh For Windows
About key pairs
Key pairs refer to the public and private key files that are used by certain authentication protocols.
Openssh.com
SSH public-key authentication uses asymmetric cryptographic algorithms to generate two key files – one 'private' and the other 'public'. The private key files are the equivalent of a password, and should stay protected under all circumstances. If someone acquires your private key, they can log in as you to any SSH server you have access to. The public key is what is placed on the SSH server, and may be shared without compromising the private key.
When using key authentication with an SSH server, the SSH server and client compare the public keys for username provided against the private key. If the server-side public key cannot be validated against the client-side private key, authentication fails.
Multi-factor authentication may be implemented with key pairs by requiring that a passphrase be supplied when the key pair is generated (see key generation below).During authentication the user is prompted for the passphrase, which is used along with the presence of the private key on the SSH client to authenticate the user.
Host key generation
Public keys have specific ACL requirements that, on Windows, equate to only allowing access to administrators and System.To make this easier,
- The OpenSSHUtils PowerShell module has been created to set the key ACLs properly, and should be installed on the server
- On first use of sshd, the key pair for the host will be automatically generated. If ssh-agent is running, the keys will be automatically added to the local store.
To make key authentication easy with an SSH server, run the following commands from an elevated PowerShell prompt:
Since there is no user associated with the sshd service, the host keys are stored under ProgramDatassh.
User key generation
To use key-based authentication, you first need to generate some public/private key pairs for your client.From PowerShell or cmd, use ssh-keygen to generate some key files.
This should display something like the following (where 'username' is replaced by your user name)
You can hit Enter to accept the default, or specify a path where you'd like your keys to be generated.At this point, you'll be prompted to use a passphrase to encrypt your private key files.The passphrase works with the key file to provide 2-factor authentication.For this example, we are leaving the passphrase empty.
Now you have a public/private ED25519 key pair(the .pub files are public keys and the rest are private keys):
Remember that private key files are the equivalent of a password should be protected the same way you protect your password.To help with that, use ssh-agent to securely store the private keys within a Windows security context, associated with your Windows login.To do that, start the ssh-agent service as Administrator and use ssh-add to store the private key.
After completing these steps, whenever a private key is needed for authentication from this client, ssh-agent will automatically retrieve the local private key and pass it to your SSH client.
Note
It is strongly recommended that you back up your private key to a secure location,then delete it from the local system, after adding it to ssh-agent.The private key cannot be retrieved from the agent.If you lose access to the private key, you would have to create a new key pairand update the public key on all systems you interact with.
Deploying the public key
To use the user key that was created above, the public key needs to be placed on the server into a text file called authorized_keys under usersusername.ssh.The OpenSSH tools include scp, which is a secure file-transfer utility, to help with this.
To move the contents of your public key (~.sshid_ed25519.pub) into a text file called authorized_keys in ~.ssh on your server/host.
This example uses the Repair-AuthorizedKeyPermissions function in the OpenSSHUtils module which was previously installed on the host in the instructions above.
These steps complete the configuration required to use key-based authentication with SSH on Windows.After this, the user can connect to the sshd host from any client that has the private key.
Recently, Microsoft has released a port of OpenSSH for Windows. You can use the package to set up an SFTP/SSH server on Windows.
- Installing SFTP/SSH Server
- Connecting to the server
Advertisement
- In Settings app, go to Apps > Apps & features > Manage optional features.
- Locate “OpenSSH server” feature, expand it, and select Install.
Binaries are installed to %WINDIR%System32OpenSSH. Configuration file (sshd_config) and host keys are installed to %ProgramData%ssh (only after the server is started for the first time).
You may still want to use the following manual installation if you want to install a newer version of OpenSSH than the one built into Windows 10.
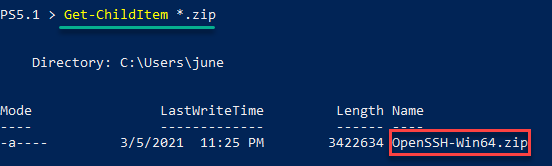
- Download the latest OpenSSH for Windows binaries (package
OpenSSH-Win64.ziporOpenSSH-Win32.zip) - As the Administrator, extract the package to
C:Program FilesOpenSSH - As the Administrator, install sshd and ssh-agent services:
- Allow incoming connections to SSH server in Windows Firewall:
- When installed as an optional feature, the firewall rule “OpenSSH SSH Server (sshd)” should have been created automatically. If not, proceed to create and enable the rule as follows.
- Either run the following PowerShell command as the Administrator:
ReplaceC:System32OpenSSHsshd.exewith the actual path to thesshd.exe(C:Program FilesOpenSSHssh.exe, had you followed the manual installation instructions above). - or go to Control Panel > System and Security > Windows Defender Firewall1 > Advanced Settings > Inbound Rules and add a new rule for port 22.
- Start the service and/or configure automatic start:
- Go to Control Panel > System and Security > Administrative Tools and open Services. Locate OpenSSH SSH Server service.
- If you want the server to start automatically when your machine is started: Go to Action > Properties. In the Properties dialog, change Startup type to Automatic and confirm.
- Start the OpenSSH SSH Server service by clicking the Start the service.
These instructions are partially based on the official deployment instructions.
Follow a generic guide for Setting up SSH public key authentication in *nix OpenSSH server, with the following difference:
- Create the
.sshfolder (for theauthorized_keysfile) in your Windows account profile folder (typically inC:Usersusername.ssh).2 - For permissions to the
.sshfolder and theauthorized_keysfile, what matters are Windows ACL permissions, not simple *nix permissions. Set the ACL so that the respective Windows account is the owner of the folder and the file and is the only account that has a write access to them. The account that runs OpenSSH SSH Server service (typicallySYSTEMorsshd) needs to have read access to the file. - Though, with the default Win32-OpenSSH configuration there is an exception set in
sshd_configfor accounts inAdministratorsgroup. For these, the server uses a different location for the authorized keys file:%ALLUSERSPROFILE%sshadministrators_authorized_keys(i.e. typicallyC:ProgramDatasshadministrators_authorized_keys).
Before the first connection, find out the fingerprint of the server’s host key by using ssh-keygen.exe for each file.
In Windows command-prompt, use:
Replace %WINDIR%System32 with %ProgramFiles%, if appropriate.
In PowerShell, use:
Replace $env:WINDIRSystem32 with $env:ProgramFiles, if appropriate.
Openssh Server

You will get an output like this:
Start WinSCP. Login dialog will appear. On the dialog:
- Make sure New site node is selected.
- On New site node, make sure the SFTP protocol is selected.
- Enter your machine/server IP address (or a hostname) into the Host name box.
- Enter your Windows account name to the User name box. It might have to be entered in the format
user@domainif running on a domain. - For a public key authentication:
- Press the Advanced button to open Advanced site settings dialog and go to SSH > Authentication page.
- In Private key file box select your private key file.
- Submit Advanced site settings dialog with the OK button.
- For a password authentication:
- Enter your Windows account password to the Password box.
- If your Windows account does not have a password, you cannot authenticate with the password authentication (i.e. with an empty password), you need to use the public key authentication.
- Save your site settings using the Save button.
- Login using Login button.
- Verify the host key by comparing fingerprints with those collected before (see above).
Advertisement
If you cannot authenticate to the server and use Windows 10 Developer mode, make sure that your OpenSSH server does not conflict with an internal SSH server used by the Developer mode. You may need to turn off the SSH Server Broker and SSH Server Proxy Windows services. Or run your OpenSSH server on a different port than 22.
- Guide to Installing Secure FTP Server on Windows using IIS;
- Guide to uploading files to SFTP server;
- Guide to automating operations (including upload).
- Windows Firewall on older versions of Windows.Back
- Windows File Explorer does not allow you to create a folder starting with a dot directly. As a workaround, use
.ssh., the trailing dot will allow you to bypass the restriction, but will not be included in the name.Back
